Edge
WAF, rate limiting, bot mitigation, TLS hygiene.
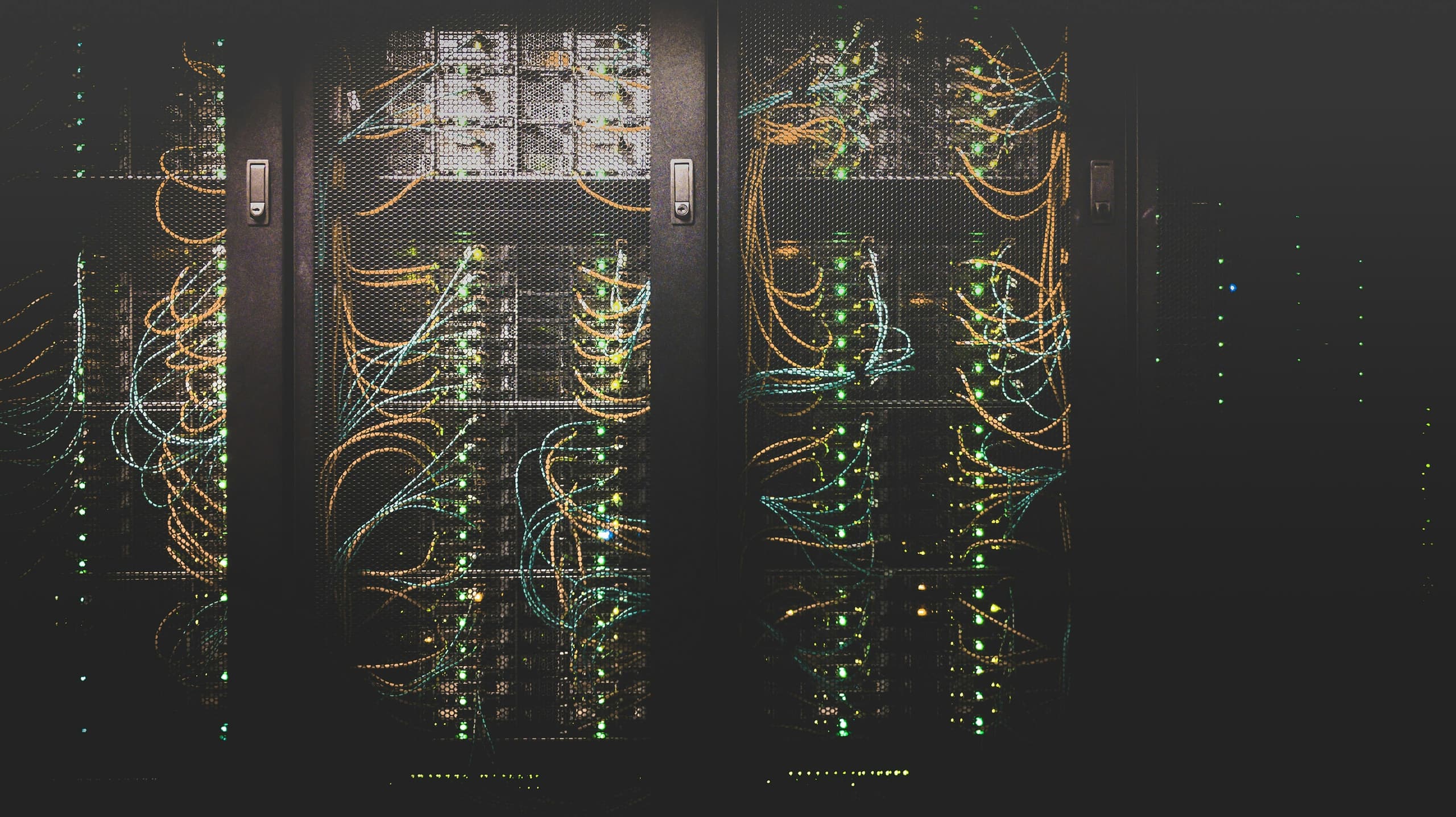
Security
Security work that survives audit because it is built, not described.
WAF, rate limiting, bot mitigation, TLS hygiene.
Authentication, authorization at every boundary, secret hygiene, dependency scanning.
Encryption at rest, key rotation, masked logging, least-privilege access.
Tested incident response, runbooks for every recurring failure mode, post-incident reviews.