View service
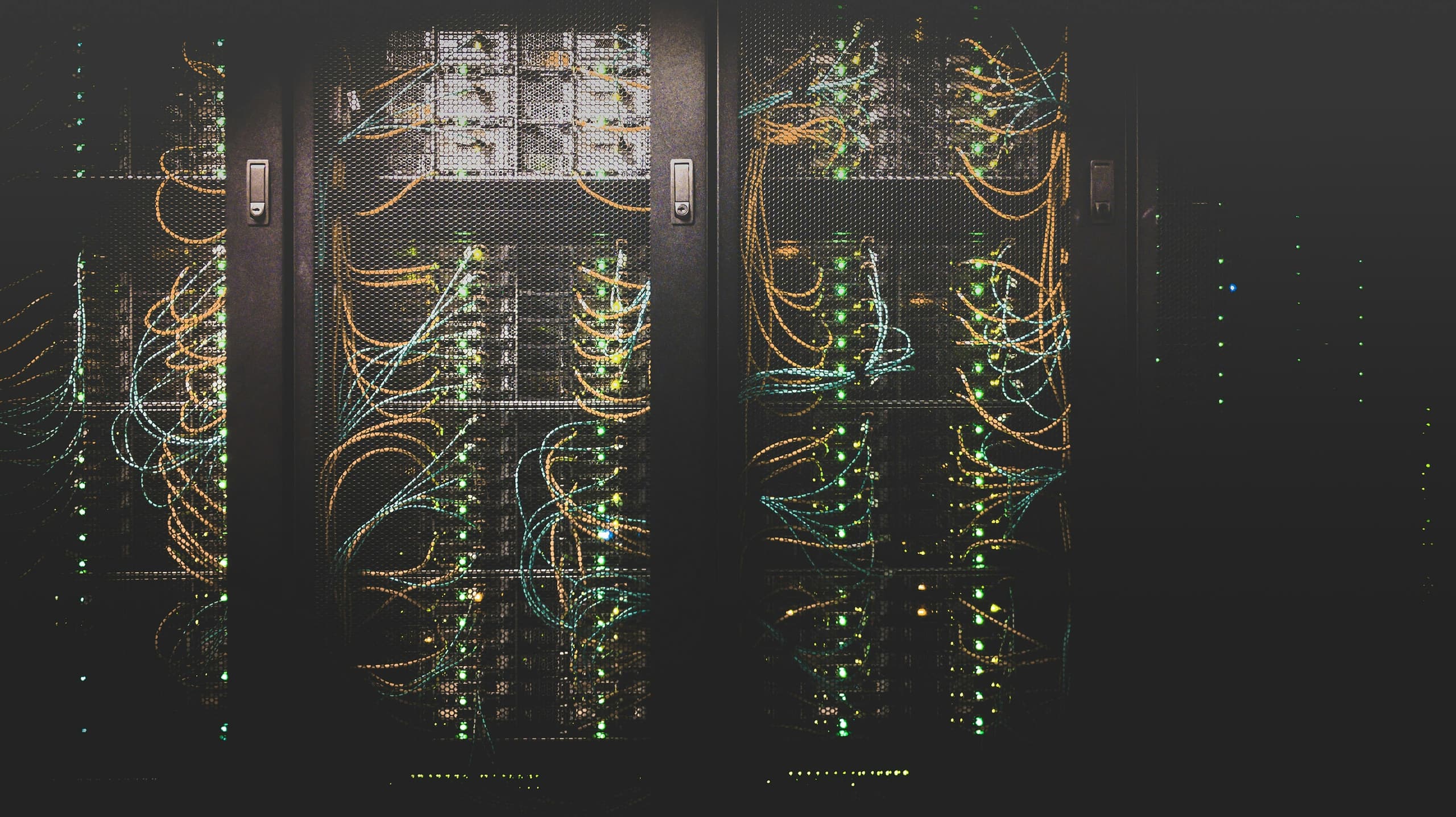
Cybersecurity
Threat modeling, secure SDLC, and operational security.
The problem
Most breaches are not novel — they exploit the same missing controls year after year.
Our approach
We embed security into the lifecycle: threat models per service, dependency monitoring, secret hygiene, and tested incident response.
Outcomes
- Threat model per service, kept current
- Automated dependency and secret scanning
- Hardened images and minimal base layers
- Incident response runbooks, exercised
Engagement process
Discover
1–2 weeks
Design
2 weeks
Build
3–10 weeks
Operate
ongoing